Data Bridge Start 813-279-5002 Revealing Trusted Contact Lookup
Data Bridge’s Trusted Contact Lookup ties account recovery and information sharing to verifiable, privacy-respecting access controls. The process emphasizes authenticated participants, minimal disclosure, and auditable activity, ensuring contacts operate within scoped permissions. Quick Connects optimize routing while balancing latency and verification, under strong encryption and transparent governance. This framework invites scrutiny of reliability, security, and practical trade-offs, as outcomes hinge on robust authentication and resilient safeguards before any data exchange can occur. The implications merit careful consideration as systems scale.
What Trusted Contact Lookup Is and Why It Matters
Trusted Contact Lookup is a mechanism that allows a user to designate trusted individuals who can receive information or assist in account recovery if the user becomes unavailable. It clarifies roles, defines procedures, and emphasizes accountability.
The concept hinges on trusted contacts and data safety, ensuring verifiable access controls, archival integrity, and minimal exposure while preserving user autonomy and streamlined restoration pathways for essential accounts.
How Data Bridge Implements Trusted Contacts Safely
Data Bridge implements Trusted Contacts safety through a structured, multi-layer approach that governs designation, verification, and access controls. The system enforces minimal disclosure by designating roles, authenticating identities, and enforcing scoped permissions. It emphasizes trusted contact privacy, ensuring data is query-restricted and auditable. Secure sharing protocols govern data exchange, encryption, and revocation, maintaining resilience against leakage without compromising user autonomy.
Real-World Use Cases: Quick Connects, Delays, and Privacy Trade-offs
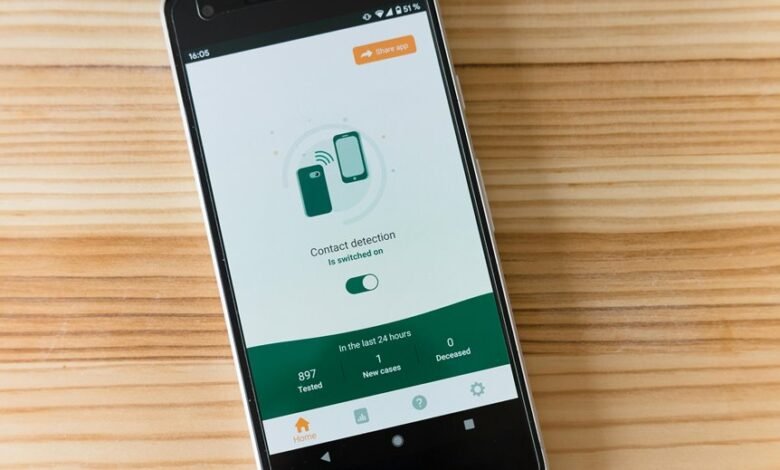
Real-world scenarios for Data Bridge’s Trusted Contacts feature illustrate how Quick Connects, intentional delays, and privacy considerations interact in practice.
In operational contexts, trusted contacts enable prioritized routing while delays balance latency with verification.
The design preserves data privacy by restricting access and auditing use, enabling controlled information sharing.
Outcomes emphasize reliability, user autonomy, and transparent governance without compromising security or confidentiality.
Evaluating Reliability, Security, and Practical Cautions
Evaluating reliability, security, and practical cautions requires a structured assessment of how Trusted Contacts perform under varied conditions, how safeguards mitigate risk, and where operational caveats may constrain use. The analysis isolates privacy implications, evaluates threat surfaces, and measures resilience against outages. Data minimization principles guide device- and credential-restrictions, ensuring timely verifications while preserving user autonomy and system integrity.
Conclusion
In the hush of encrypted channels, trusted contacts move from concept to guarded protocol. Data Bridge’s framework enforces authenticated access, minimal disclosure, and auditable trails, turning recovery and notifications into verifiable actions rather than guesses. Yet as Quick Connects race latency, hidden trade-offs emerge—privacy vs. convenience, resilience vs. exposure. The system stands on rigor and governance, awaiting practical validation under real-world pressures. The next spark of incident, and the outcome hinges on disciplined execution and unwavering verification.






