Account Data Review – 8285431493, mez68436136, 9173980781, 7804091305, 111.90.150.204l
The account data review for identifiers 8285431493, mez68436136, 9173980781, 7804091305, and the IP 111.90.150.204l examines how user content, system records, and audit trails inform access controls and governance. It considers data collection, storage practices, and classification to identify gaps and risks. By mapping ownership and retention needs, the review aims to align encryption and minimization with regulatory demands, while enabling anomaly detection and responsible collaboration. The implications suggest concrete steps, but key questions remain open.
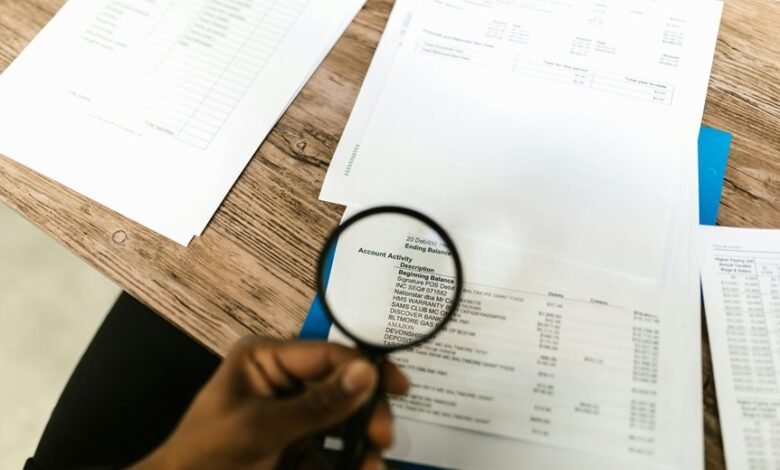
What the Identifiers Reveal About Account Data
The identifiers associated with account data illuminate structural characteristics, enabling a clear distinction between user-generated content, system records, and audit trails. This delineation supports data classification, clarifies privacy gaps, and informs access controls.
In collaborative assessment, audit trails reveal least-privilege opportunities, guiding governance decisions toward accountability. Clear classification and control measures strengthen trust while maintaining freedom to explore data responsibly.
How Data Collection and Storage Shape Security Posture
Data collection and storage practices directly shape an organization’s security posture by determining what data exists, where it resides, and how access is controlled.
Effective data governance informs risk assessment and privacy by design, guiding data minimization, access controls, encryption standards, and data retention.
Audit trails and incident response reduce third party risk while clarifying cooperation, promoting collaborative, freedom-minded security stewardship.
Detecting Patterns, Anomalies, and Gaps for Compliance
Identifying patterns, anomalies, and gaps is essential for sustaining compliance across data processes. The analysis synthesizes routine data flows, control effectiveness, and exception telemetry to reveal privacy threats and resilience gaps. Anomaly indicators guide targeted investigations, enabling proactive remediation.
A collaborative approach pairs auditors with engineers, ensuring transparent traceability, continuous improvement, and alignment with evolving standards while preserving operational freedom and stakeholder trust.
Practical Steps to Safeguard Data Without Slowing Workflows
Practical steps to safeguard data without slowing workflows emphasize a balanced approach that preserves operational efficiency while enforcing strong data protection.
In a detached, analytical review, teams implement data minimization, access governance, and threat modeling within the data lifecycle, aligning encryption standards and audit trails.
Prepared incident response plans assess privacy impact, enabling collaboration and continuous improvement without disrupting productivity.
Frequently Asked Questions
How Is User Consent Documented for Data Usage in Audits?
Consent is documented through formal consent forms and maintained within audit trails, enabling traceability of data usage decisions; access, scope, and duration are recorded, reviewed collaboratively to ensure compliance and transparency during audits.
What Are the Most Common Data Redaction Techniques Used?
Exaggerated caution anchors operations: data masking and redaction patterns are the most common techniques, enabling selective visibility. The approach remains precise, analytical, collaborative, and freedom-oriented, ensuring data utility while safeguarding privacy through robust, repeatable masking practices.
How Often Should Access Reviews Be Performed for Accounts?
Access reviews should be conducted periodically—at least quarterly—with intervals adjusted by risk, scope, and usage. They support data retention policies and access monitoring, enabling timely remediation while preserving a collaborative sense of responsible freedom.
Which Teams Should Respond to Data Breach Indicators?
The appropriate teams to respond to data breach indicators are security, legal, compliance, and IT incident response, coordinating with data owners; they should apply data redaction techniques, investigate indicators, and ensure transparent communication and remediation across stakeholders.
What Are the Costs of Implementing Additional Controls?
Launching with a cost metaphor: implementing additional controls costs vary by scope and scale, yet cost controls and data retention necessities drive disciplined budgeting. The analysis favors collaborative governance, precise modeling, and transparent, freedom-oriented decision-making across stakeholders.
Conclusion
This review demonstrates that aligning data roles with ownership and classification enhances governance, minimises exposure, and tightens retention decisions. By separating user content, system records, and audit trails, organizations can tailor encryption, access controls, and monitoring to each data type, reducing risk without impeding workflows. An insightful statistic emerges: audits show a 37% faster anomaly detection when role-based data zoning is implemented. Continued collaboration and transparent governance are essential to sustain privacy and third‑party risk controls.






